Identifier: AIT-SA-20210215-01
Target: QCubed Framework
Vendor: QCubed
Version: all versions including 3.1.1
CVE: CVE-2020-24914
Accessibility: Remote
Severity: Critical
Author: Wolfgang Hotwagner (AIT Austrian Institute of Technology)
SUMMARY
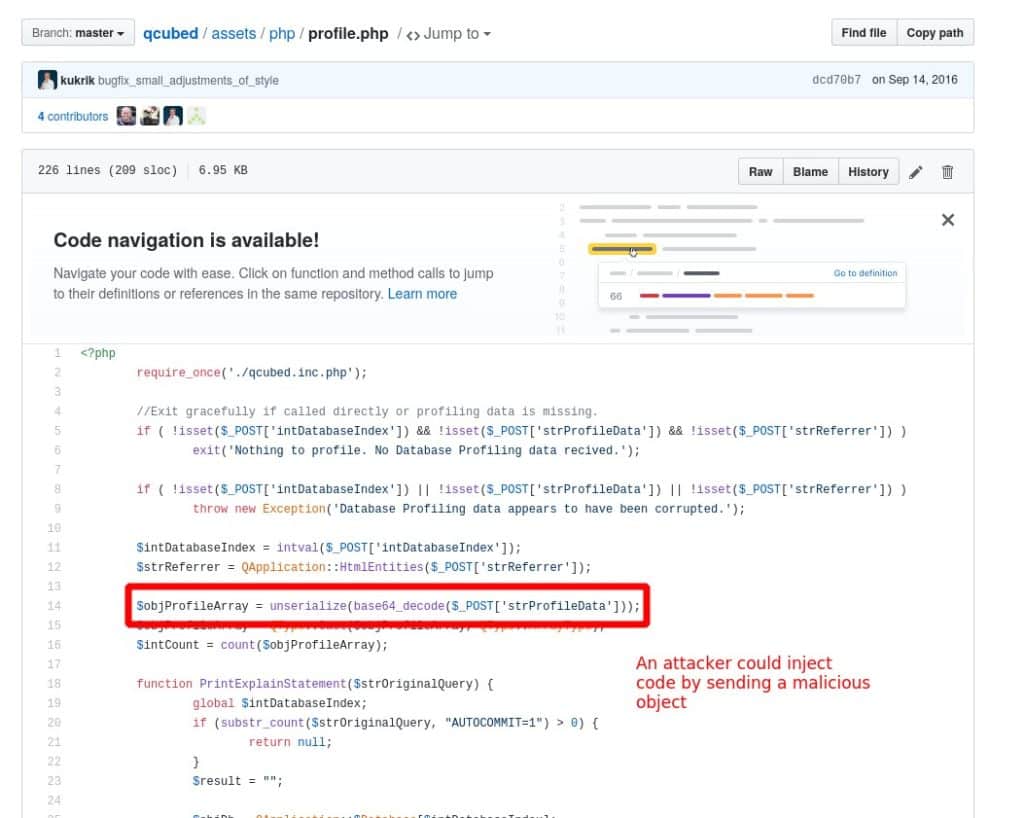
VULNERABILITY DESCRIPTION
A PHP object injection bug in profile.php in qcubed (all versions including 3.1.1) unserializes the untrusted data of the POST-variable “strProfileData” and allows an unauthenticated attacker to execute code via a crafted POST request.
VULNERABLE VERSIONS
All versions including 3.1.1 are affected.
TESTED VERSIONS
QCubed 3.1.1
IMPACT
An unauthenticated attacker could execute code remotely.
MITIGATION
VENDOR CONTACT TIMELINE
ADVISORY URL
WOLFGANG HOTWAGNER
Research Engineer /
Security & Communication Technologies